Blog
Key Strategies to Cope with a Limited IT Budget
You understand the need for a solid IT plan. You know the security risks and how they apply to your company. You want your employees to have the best tools available so they can do their jobs as productively as possible. But you don’t have an unlimited budget. How...
Data Loss Prevention Is About People and Strategy
Your data is one of your organization’s most valuable assets—perhaps even the most valuable. The problem is that there are many threats that can cause catastrophic data loss, including social engineering attacks, ransomware (and...
The Deep Web, The Dark Web, and Why You Should Care
From time to time, the news shouts about some company that had their data security breached and warns consumers that their information may have been leaked. But leaked where? Who wants the information and how do they get it? There are assorted answers to these...
3 Signs of a Great Remote Work Culture
Have you ever wondered what the difference between good companies and great companies is? In many cases, it’s their culture. Tony Hsieh, the retired CEO of the online shoe and clothing company Zappos, even believes that most of the other stuff takes care of itself...
Confusing Business Technology Terms Explained
We walk around all the time talking about the internet or the web, but did you know that there’s a difference? And that UI and UX are commonly interchanged, but they mean very different things? Here’s another one: Memory is not the same as disc space. Gets confusing...
Important Remote Work Mistakes to Avoid
A lot has been said and written about the benefits of transitioning to remote work since the pandemic made it impossible for many organizations to operate from a single, physical location. Whether enthusiastically or begrudgingly, many employees have made the shift,...
Email Etiquette Tips You Should Never Forget
These days more and more of our interactions are written out, whether in emails, instant messaging, or text messaging. Since we find ourselves writing more and more, it’s tempting to find ways to cut corners in an attempt to get more done. But at what cost? All...
Small Businesses Are Waging a Digital War for Customers
The way customers engage with businesses is constantly evolving. In today’s digital-first world, customers are always just a few clicks away from meeting their needs. And with the pandemic increasing concerns about in-person transactions, most consumers and business...
Common Compliance Issues Faced by Remote Employees
Since health safety guidelines changed the workplace, many employees have experienced what they had only read about before: the benefits of remote work. Their employers, on the other hand, are losing sleep over compliance. Remote Work Compliance Issues Won’t Go Away...
Advanced Outlook Tips for Expert Email Management
Workers who have used Outlook for years are typically familiar with These are some of our favorite tricky tips, but a word of warning: creating too many folders and automations (like those that rules take care of) can eventually create more issues than solve them. Be...
Outlook Tips for Better Email Management
Some days, incoming emails just won’t slow down. And if you’re trying to meet a deadline or focus on a customer issue, scanning each one for critical issues can be a part-time job that delays everything else. Even for people who continuously use the four “D”s of email...
How to Grow a Positive Remote Work Culture
The pandemic threw (and is still throwing) many curveballs at small businesses. One of the most impactful was the shift from onsite to remote work models. But as stated, that was only one. With so many other issues to face—like new technology needs and customer access...
What Is Cyber Liability Insurance and Why Is It Important for Small Business?
Nobody likes paying for insurance, but one of the hard facts of owning a business is that there is an array of insurance that must be maintained (and provided, but that’s a different topic). One that is often overlooked by small business—but can actually be more...
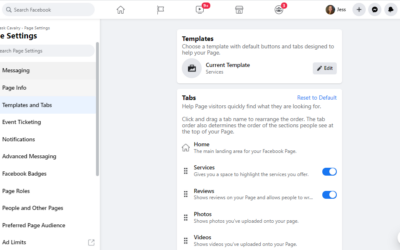
Which Facebook business page template you should use and why
If you haven’t created a business page for your company on Facebook, do it now. Open a new tab in your browser and go to https://www.facebook.com, then use the set up wizard to complete all the necessary steps (you always edit anything later). Seriously. It’s far more...
Biggest Benefits of VoIP for Small Business
Most services associated with operating expenses are going virtual these days. Which is good news for businesses who are considering Voice over Internet Protocol (VoIP). Even though this technology has been around since 1995, advancements in service and functionality...
Top Tech Trends for Small Business in 2021
It’s safe to say that 2020 was one of the unruliest years in recent memory. The pandemic decimated entire industries, forced many businesses around the world to close their doors, and reminded everyone that survival depends on the ability to adapt and innovate. Even...
How Multitasking is Hurting Your Job Performance (and health)
Since more and more people work remotely, psychological studies are emerging that dig into the real implications of bad work habits. And since lion’s share of schools and companies don’t teach us how to be an effective worker (only how to work), we are left to our own...
Holiday Tech Reminders for Working from Home (BONUS: gift ideas!)
Even those of us who work from the office are probably finding more reasons than just the pandemic to work from home this month. The weather is turning colder, and the coming holidays are bringing their own considerations. So, since everyone is getting cozier and...
Excel Tips for Beginners and Casual Users (with screenshots)
Excel is a vast universe of tools that are all designed to store, organize, and (most importantly) manipulate data. For anyone who’s used the program, it’s pretty apparent from the start that even a user working in it for a few years probably only scratches the...
Multi-factor Authentication: Why it’s here, what it is, and why you need it
Why do I keep hearing about multi-factor authentication? Have you noticed that the minimum requirements for a new password are getting more and more complex these days? Even on simple websites like your local florist or your online neighborhood watch group, security...
How a Computer Network Actually Works
If you’re reading this article, it means that your device is connected to a computer network. Networks like the one you’re connected to right now have transformed the way we communicate, access information, and work. But just like most everything in the world of...
How to Use Google Alerts to Grow Your Business (and how to set them up)
Google Alerts are great for small businesses who don’t have much (if any) of a marketing workforce. Oddly though, they’re rarely leveraged until a savvy marketing shows up and turns them on. Small business owners and salespeople typically aren’t educated about how...
Why Everyone (yes, everyone) Needs Antivirus Software
If you lived in a bad area, would you leave the front door to your house unlocked? Of course not! When it comes to the “house” that your data is stored in (i.e. your computer), you can think of the internet as one huge bad neighborhood, and no computer that’s...
Advanced and easy tips for Word that will make you a document master
Word is a program that most data workers can't live without. It's easy to use interface and intuitive layout makes it faster to learn than other word processing software out there. Plus, since it's a part of the Microsoft Office 365 suite, it's already integrated into...